Academics
Assoc. Prof. Nhien-An Le-Khac
School of Computer Science, University College Dublin
Nhien-An Le-Khac is an Associate Professor at the School of Computer Science, University College Dublin (UCD). He is currently the Programme Co-Director of UCD’s MSc programme in Forensic Computing and Cybercrime Investigation (MSc FCCI), an international programme for law enforcement officers specialising in cybercrime investigation.
His research interests span cloud security and forensics, data privacy, data mining for financial services, and fraud and criminal detection. He is the principal author or co-author of more than 70 scientific papers in international, peer-reviewed journals and conferences in related disciplines.
Research Output
Publications
Ensuring Cross-Device Portability of Electromagnetic Side-Channel Analysis for Digital Forensics
Forensic Science International: Digital Investigation Vol. 48 pp. 301684
This study investigates the cross-device portability of Electromagnetic Side-Channel Analysis (EM-SCA) for digital forensics, exploring its applicability to various smart devices. The authors experiment with different devices, including iPhones and Nordic Semiconductor nRF52-DK, and demonstrate the effectiveness of transfer learning techniques in achieving high accuracy.
Data Exfiltration through Electromagnetic Covert Channel of Wired Industrial Control Systems
Applied Sciences Vol. 13 pp. 2928
This study demonstrates a novel attack vector on industrial control systems (ICS) that leverages electromagnetic (EM) radiation from wired Ethernet connections to exfiltrate sensitive information. The attack exploits compromised firmware to encode data into packet transmission patterns, which are then captured and demodulated by an attacker's software-defined radio. This covert channel facilitates data exfiltration from up to two meters away with a 10 bps data rate.
Identifying Internet of Things Software Activities using Deep Learning-based Electromagnetic Side-Channel Analysis
Forensic Science International: Digital Investigation Vol. 39 pp. 301308
This study explores the application of machine learning techniques to identify complex activities on IoT devices using electromagnetic side-channel analysis. The researchers created a dataset by running ten sorting algorithms on an Arduino device and used it to train various classification models, including deep learning models. The results show that convolutional neural networks can accurately predict the activity being executed with a high level of accuracy (99.6%).
A Comparative Study of Support Vector Machine and Neural Networks for File Type Identification Using n-gram Analysis
Forensic Science International: Digital Investigation
This study compares the performance of Support Vector Machines (SVMs) and Neural Networks (NNs) for file type identification using n-gram analysis. The authors investigate the influence of input parameters, such as learning rate and n-gram values, on the results and compare the scalability of SVMs and NNs. The study finds that SVM-based approaches perform better than NNs, but their scalability is still a challenge.
Retracing the Flow of the Stream: Investigating Kodi Streaming Services
The 11th EAI International Conference on Digital Forensics and Cyber Crime
This paper presents a new method for quickly locating Kodi artifacts and gathering information for successful prosecution of digital piracy and streaming of illegal content. The approach is evaluated on Windows, Android, and Linux platforms, demonstrating the location of file artifacts, databases, and viewed content history.
SoK: Exploring the State of the Art and the Future Potential of Artificial Intelligence in Digital Forensic Investigation
The 13th International Workshop on Digital Forensics (WSDF), held at the 15th International Conference on Availability, Reliability and Security (ARES)
This systematic overview of artificial intelligence (AI) in digital forensic investigation explores the current state of the art and future potential of AI in expediting digital forensic analysis and increasing case processing capacities. The authors discuss AI applications in data discovery, device triage, and other areas, highlighting current challenges and future directions.
Facilitating Electromagnetic Side-Channel Analysis for IoT Investigation: Evaluating the EMvidence Framework
Forensic Science International: Digital Investigation
This paper presents the EMvidence framework, a software tool that facilitates electromagnetic side-channel analysis for IoT investigation. The framework automates and simplifies the process of acquiring and analyzing electromagnetic signals from IoT devices, making it accessible to digital forensic investigators without specialized equipment or expertise.
Assessing the Influencing Factors on the Accuracy of Underage Facial Age Estimation
The 6th IEEE International Conference on Cyber Security and Protection of Digital Services (Cyber Security)
This study evaluates the influencing factors on the accuracy of underage facial age estimation using two cloud services, Microsoft Azure's Face API and Amazon Web Service's Rekognition service. The analysis of the VisAGe dataset reveals correlations between facial attributes and age estimation errors, identifying the most significant factors to be addressed in future age estimation modeling.
Cutting through the Emissions: Feature Selection from Electromagnetic Side-Channel Data for Activity Detection
Forensic Science International: Digital Investigation Vol. 32 pp. 300927
This paper presents a systematic methodology to identify information leaking frequency channels from high dimensional EM data using multiple filtering techniques and machine learning. The approach is evaluated on a dataset of EM signals from an IoT device, demonstrating its effectiveness in reducing the number of channels from 20,000 to less than 100, improving real-time analysis efficiency.
DeepUAge: Improving Underage Age Estimation Accuracy to Aid CSEM Investigation
Forensic Science International: Digital Investigation Vol. 32 pp. 300921
DeepUAge improves underage age estimation accuracy to aid Child Sexual Exploitation Material (CSEM) investigation. The model, trained on the VisAGe dataset, achieves state-of-the-art performance for age estimation of minors, with a mean absolute error (MAE) rate of 2.73 years. This work tackles the challenges of collecting and annotating underage facial age data, and its application can expedite digital investigations.
EMvidence: A Framework for Digital Evidence Acquisition from IoT Devices through Electromagnetic Side-Channel Analysis
Forensic Science International: Digital Investigation Vol. 32 pp. 300907
This paper presents EMvidence, a software framework for digital forensic investigators to acquire evidence from IoT devices through electromagnetic side-channel analysis. The framework automates and performs electromagnetic side-channel evidence collection, making it a practical reality for digital forensic investigators.
Improving Borderline Adulthood Facial Age Estimation through Ensemble Learning
The 8th International Workshop on Cyber Crime (IWCC), held at the 14th International Conference on Availability, Reliability and Security (ARES)
This paper presents an ensemble learning approach to improve facial age estimation for borderline adulthood cases. The authors develop a deep learning model (DS13K) and fine-tune it on the Deep Expectation (DEX) model to achieve an accuracy of 68% for the age group 16-17 years old, outperforming DEX by 4 times. The study also evaluates existing cloud-based facial age prediction services.
A Survey of Electromagnetic Side-Channel Attacks and Discussion on their Case-Progressing Potential for Digital Forensics
Digital Investigation Vol. 29 pp. 43-54
This paper surveys electromagnetic side-channel attacks and their potential for digital forensics on IoT devices. It discusses the challenges of analyzing encrypted data from IoT devices and explores the use of electromagnetic side-channel analysis to recover cryptographic keys and other sensitive information.
Leveraging Electromagnetic Side-Channel Analysis for the Investigation of IoT Devices
Digital Investigation
This paper presents a novel methodology to inspect the internal software activities of IoT devices through their electromagnetic radiation emissions during live device investigation. The approach uses electromagnetic side-channel analysis (EM-SCA) to detect software activities, including cryptographic algorithms and malicious modifications, with high accuracy.
Improving the Accuracy of Automated Facial Age Estimation to Aid CSEM Investigations
Digital Investigation Vol. 28 pp. S142
This study evaluates existing age prediction services and introduces a deep learning model, DS13K, to improve the accuracy of underage facial age estimation in child sexual exploitation material (CSEM) investigations. The model outperforms existing services, particularly in the borderline adulthood age range (16-17 years old), with an accuracy rate of 68%.
Shining a light on Spotlight: Leveraging Apple's desktop search utility to recover deleted file metadata on macOS
Digital Investigation
This study examines Apple's desktop search technology, Spotlight, to recover deleted file metadata on macOS. Researchers developed a novel approach to extract persistent records of deleted files directly from the Spotlight database and recover records from deleted database pages in unused space. The study provides a proof-of-concept implementation and discusses the forensic opportunities offered by recovering records for deleted files within the database and unused space on the filesystem.
Solid State Drive Forensics: Where Do We Stand?
Digital Forensics and Cyber Crime pp. 149-164
This paper examines the current state of solid-state drive (SSD) forensics, addressing the challenges posed by SSDs' background data movement and garbage collection processes. The authors investigate the impact of TRIM, data volume, and powered-on time on data recovery and provide guidance on extracting artefacts from SSDs under various conditions.
Accuracy Enhancement of Electromagnetic Side-channel Attacks on Computer Monitors
The Second International Workshop on Criminal Use of Information Hiding (CUING), part of the 13th International Conference on Availability, Reliability and Security (ARES)
This paper investigates the accuracy of electromagnetic side-channel attacks on computer monitors, focusing on factors beyond sampling rate and bandwidth. The authors evaluate noise removal, image blending, and image quality adjustments to improve image reconstruction accuracy, exploring avenues for future improvements in EM side-channel attacks.
Enabling the Non-Expert Analysis of Large Volumes of Intercepted Network Traffic
Advances in Digital Forensics XIV pp. 183-197
This paper proposes a novel approach to analyze large volumes of intercepted network traffic based on network metadata, reducing analysis duration and providing insights for non-technical investigators. The approach is tested with a large sample of network traffic data and can be used to identify devices and usage behind an internet connection.
Digital Forensic Investigation of Two-Way Radio Communication Equipment and Services
Digital Investigation Vol. 26S pp. xx-xx
This study investigates the digital forensic traces in modern two-way radio communication equipment and services, which is crucial for law enforcement in crime investigations. The research proposes a novel workflow for investigators to follow when encountering such equipment, highlighting the need for knowledge about radio communication equipment, infrastructure, and associated services.
Digital Forensic Investigation of Two-Way Radio Communication Equipment and Services
Digital Investigation Vol. 26 pp. S77 - S86
This paper investigates the digital forensic investigation of two-way radio communication equipment and services, including the acquisition and analysis of digital traces in modern radio communication devices. The authors propose a workflow for radio device investigation and evaluate the possibility of using popular forensic tools to acquire artefacts from radio communication equipment.
Electromagnetic Side-Channel Attacks: Potential for Progressing Hindered Digital Forensic Analysis
Proceedings of the International Workshop on Speculative Side Channel Analysis (WoSSCA 2018)
This paper explores the potential of electromagnetic side-channel analysis in progressing hindered digital forensic investigations. The authors argue that EM side-channel attacks can provide a hands-off approach to accessing internal device information, overcoming encryption and limited standardization of IoT devices.
Evaluating Automated Facial Age Estimation Techniques for Digital Forensics
12th International Workshop on Systematic Approaches to Digital Forensics Engineering (SADFE), IEEE Security & Privacy Workshops
This paper evaluates existing automated facial age estimation techniques for digital forensics, highlighting their limitations and proposing a dataset generator to overcome the lack of sufficient sample images in specific age ranges. The study assesses the performance of offline and cloud-based models, releasing a tool to generate uniformly distributed random images by age and gender.
Private Web Browser Forensics: A Case Study on Epic Privacy Browser
Journal of Information Warfare Vol. 17
This study examines the Epic Privacy Browser, a private web browser designed to protect users' privacy, and its potential for forensic analysis. The researchers investigate the types of evidence left behind by the browser on Windows 10 and Windows 7 operating systems, including live and post-mortem analysis. The study aims to identify the tools and methods for effective analysis of the browser's artefacts.
Privileged Data within Digital Evidence
Proceedings of the 16th IEEE International Conference On Trust, Security And Privacy In Computing And Communications (TrustCom-17) pp. 737-744
This paper presents a script for handling privileged data in digital forensic tools, specifically in Nuix, to minimize exposure to investigators and automate the filtering process. The script increases effectiveness by relating files based on content, addressing the limitations of traditional filtering methods.
Evaluation of Digital Forensic Process Models with Respect to Digital Forensics as a Service
Proceedings of the 16th European Conference on Cyber Warfare and Security (ECCWS 2017) pp. 573-581
This paper evaluates the applicability of existing digital forensic process models to a cloud-based evidence processing paradigm, specifically Digital Forensics as a Service (DFaaS). The authors analyze the characteristics of each current process model and review the benefits of DFaaS, aiming to expedite the investigative process and reduce costs.
Forensic Analysis of Epic Privacy Browser on Windows Operating Systems
Proceedings of the 16th European Conference on Cyber Warfare and Security (ECCWS 2017) pp. 341-350
This paper presents a forensic analysis of Epic Privacy Browser on Windows operating systems, focusing on the identification and analysis of artefact evidence left on Windows 10 compared to Windows 7. The study aims to establish if the introduction of Windows 10 has had an adverse effect on the browser's claim of clearing all user activity traces upon closure.
Integration of Ether Unpacker into Ragpicker for plugin-based Malware Analysis and Identification
Proceedings of the 16th European Conference on Cyber Warfare and Security (ECCWS 2017) pp. 419-425
This paper presents a new approach to malware analysis by integrating Ether Unpacker into the plugin-based malware analysis tool, Ragpicker. The integration aims to improve the unpacking rate of malware samples, enabling the analysis of transferred and reused code. The authors evaluate their approach against real-world malware patterns, demonstrating its effectiveness in identifying malware variants and families.
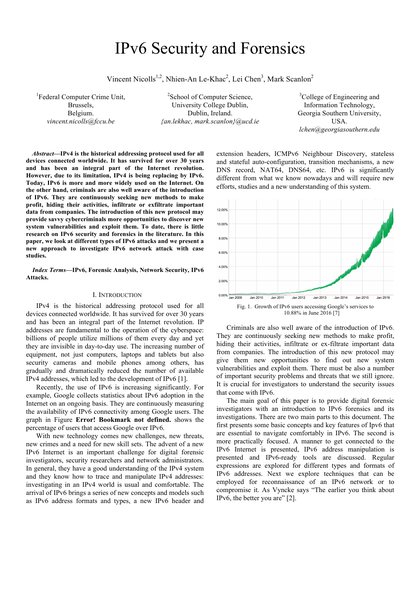
IPv6 Security and Forensics
2nd International Workshop on Cloud Security and Forensics (WCSF 2016) pp. 743-748
This paper presents a new approach to investigate IPv6 network attacks with case studies, focusing on IPv6 security and forensics. It discusses different types of IPv6 attacks and provides a comprehensive overview of IPv6 network attack techniques, including reconnaissance, exploitation, and mitigation strategies.
An Analytical Approach to the Recovery of Data From 3rd Party Proprietary CCTV File Systems
15th European Conference on Cyber Warfare and Security (ECCWS 2016)
This paper presents an analytical approach to recovering data from 3rd party proprietary CCTV file systems, focusing on a Ganz CCTV DVR model C-MPDVR-16. The authors reverse engineer the proprietary file system, enabling the retrieval of the oldest video footage possible. The method is evaluated using a case study, demonstrating the feasibility of recovering video footage from a DVR with no initial knowledge or documentation available.
Increasing Digital Investigator Availability through Efficient Workflow Management and Automation
The 4th International Symposium on Digital Forensics and Security (ISDFS 2016) pp. 68-73
This paper proposes a workflow management automation framework to streamline digital investigation workflows, reducing time spent on acquisition and preparation steps, and increasing efficiency of forensic software and hardware use. The framework is evaluated in a real-world scenario, demonstrating its benefits and robustness.
Tiered Forensic Methodology Model for Digital Field Triage by Non-Digital Evidence Specialists
Digital Investigation Vol. 16 pp. 75-85
This paper presents a tiered forensic methodology model for digital field triage by non-digital evidence specialists. The model aims to increase investigation efficiency and reduce the backlog of digital evidence waiting for analysis by trained specialists. The authors propose a framework for training front-line investigators to conduct digital field triage, allowing them to provide actionable information quickly and maintain the integrity of digital evidence.
Overview of the Forensic Investigation of Cloud Services
10th International Conference on Availability, Reliability and Security (ARES 2015) pp. 556-565
This paper provides an overview of the forensic investigation of cloud services, discussing the challenges and opportunities of cloud computing in digital forensics. It examines the state-of-the-art in cloud-focused digital forensic practices, including the collection and analysis of evidence, and the potential use of cloud technologies to provide Digital Forensics as a Service.
Towards the Forensic Identification and Investigation of Cloud Hosted Servers through Noninvasive Wiretaps
Proceedings of 10th International Conference on Availability, Reliability and Security (ARES 2015)
This paper presents a new approach to rapidly and reliably identify cloud-hosted servers through non-invasive wiretaps. A handheld device composed of an embedded computer and a method of undetectable Ethernet-based communication interception is developed and tested. The device captures minimal information and only stores relevant data, with an audit log of operator actions for reporting.