Directors
Assoc. Prof. Mark Scanlon
School of Computer Science, University College Dublin
Mark Scanlon is an Associate Professor in University College Dublin’s (UCD’s) School of Computer Science and Founding Director of the Forensics and Security Research Group. He is a Fulbright Scholar in Cybersecurity and Cybercrime Investigation.
His research interests sit at the intersection of digital forensics, cybersecurity, and applied AI, developing and rigorously evaluating methods and tools that make digital evidence acquisition and analysis more efficient, automated, reliable, and reproducible. He is a Senior Editor for Elsevier’s Forensic Science International: Digital Investigation journal, and is a keen reviewer and conference organiser in the field. He is a member of the Board of Directors of Digital Forensics Research Workshop Inc. (DFRWS), a US 501(c) non-profit organisation responsible for defining and advancing the field of digital forensic science.
Research Output
Publications
Objects as Universal Geolocation Cues: A Computer Vision Approach
13th Annual Digital Forensics Research Workshop Europe (DFRWS EU 2026)
This paper proposes a computer vision approach to geolocation using universal visual cues, specifically electrical plug sockets, to narrow down the search space for law enforcement in combating crimes such as human trafficking and child exploitation.
AutoDFBench 1.0: A benchmarking framework for digital forensic tool testing and generated code evaluation
Forensic Science International: Digital Investigation Vol. 56 pp. 302055
AutoDFBench 1.0 is a benchmarking framework for digital forensic tool testing, evaluating conventional and AI-generated tools across five areas: string search, deleted file recovery, file carving, Windows registry recovery, and SQLite data recovery.
Investigation of large language models, GenAI, and proprietary AI systems: Digital forensic evidence, readiness and regulation
Forensic Science International: Digital Investigation Vol. 57 pp. 302135
This paper investigates digital forensic evidence and regulation of large language models and proprietary AI systems, highlighting the need for AI forensic readiness and examinability.
Plug to place: Indoor multimedia geolocation from electrical sockets for digital investigation
Forensic Science International: Digital Investigation Vol. 56 pp. 302056
This paper introduces a pipeline for indoor multimedia geolocation using electrical sockets as consistent markers, aiding law enforcement in human trafficking investigations.
VAAS: Vision-Attention Anomaly Scoring for image manipulation detection in digital forensics
Forensic Science International: Digital Investigation Vol. 56 pp. 302063
VAAS detects image manipulation using Vision Transformers and segmentation embeddings, providing a continuous anomaly score for digital forensics.
Towards a standardized methodology and dataset for evaluating LLM-based digital forensic timeline analysis
Forensic Science International: Digital Investigation Vol. 54S pp. 301982
This paper proposes a standardized methodology for evaluating the performance of Large Language Models (LLMs) in digital forensic timeline analysis tasks, such as event summarization. The methodology includes a dataset, timeline generation, and ground truth development, and recommends the use of BLEU and ROUGE metrics for quantitative evaluation.
An AI-Based Network Forensic Readiness Framework for Resource-Constrained Environments
Proceedings of the 18th International Workshop on Digital Forensics, part of the 20th International Conference on Availability, Reliability and Security
This paper presents an AI-based network forensic readiness framework for resource-constrained environments. The framework integrates optimised artificial intelligence models to detect attacks in real-time, capturing and preserving critical forensic artefacts. It aligns with ISO/IEC 27043:2015 Digital Forensic Readiness principles, reducing time and human effort.
Fine-Tuning Large Language Models for Digital Forensics: Case Study and General Recommendations
ACM Digital Threats: Research and Practice pp. 3748264
This paper proposes recommendations for fine-tuning large language models (LLMs) for digital forensics tasks, addressing the gap in existing research. A case study on chat summarization showcases the applicability of the recommendations, evaluating multiple fine-tuned models to assess their performance. The study shares lessons learned from the case study, providing insights into the fine-tuning process, computational power issues, data challenges, and evaluation methods.
AutoDFBench: A Framework for AI Generated Digital Forensic Code and Tool Testing and Evaluation
Digital Forensics Doctoral Symposium
AutoDFBench is an automated framework for testing and evaluating AI-generated digital forensic code and tools. It validates AI-generated code against NIST''s Computer Forensics Tool Testing Program (CFTT) procedures and calculates a benchmarking score. The framework operates in four phases: data preparation, API handling, code execution, and result recording with score calculation.
Improving Image Embeddings with Colour Features in Indoor Scene Geolocation
IEEE Access Vol. 13
This paper proposes a model architecture that integrates image N-dominant colours and colour histogram vectors with image embedding from deep metric learning and classification perspectives to improve image geolocation in indoor scenes.
Low-overhead and Non-invasive Electromagnetic Side-Channel Monitoring for Forensic-ready Industrial Control Systems
Digital Forensics Doctoral Symposium
This paper proposes a low-overhead and non-invasive electromagnetic side-channel monitoring approach for forensic-ready industrial control systems. It uses unintentional electromagnetic radiation emitted by Ethernet network cables to detect denial of service attacks with considerable accuracy, introducing an architecture for ICS infrastructure to be forensic-ready with minimal computational resources.
Exploring the Potential of Large Language Models for Improving Digital Forensic Investigation Efficiency
Forensic Science International: Digital Investigation Vol. 52 pp. 301859
This study explores the potential of Large Language Models (LLMs) in improving digital forensic investigation efficiency, addressing challenges such as bias, explainability, censorship, and resource-intensive infrastructure. A comprehensive literature review highlights the current challenges in digital forensics and the possibilities of incorporating LLMs, with a focus on established models, methods, and key challenges.
Context Based Password Cracking Dictionary Expansion Using Generative Pre-trained Transformers
2024 Cyber Research Conference - Ireland (Cyber-RCI)
This paper explores the effectiveness of combining a strategic contextual approach with large language models in password cracking. The authors create context-based password dictionaries through training PassGPT models with contextual information, demonstrating improved password cracking efficiency and accuracy.
Perceptual Colour-based Geolocation of Human Trafficking Images for Digital Forensic Investigation
2024 Cyber Research Conference - Ireland (Cyber-RCI)
This study investigates the effectiveness of colour-based descriptors in Content-Based Image Retrieval (CBIR) for human trafficking image analysis. The research evaluates the impact of various parameters on image matching accuracy, achieving a Top-50 accuracy of over 95% on the Hotels-50K dataset. The approach demonstrates potential in advancing image analysis tools for human trafficking investigations and other contexts.
Pushing Network Forensic Readiness to the Edge: A Resource Constrained Artificial Intelligence Based Methodology
2024 Cyber Research Conference - Ireland (Cyber-RCI)
This paper introduces the Network Forensic Readiness for Edge Devices (NetFoREdge) framework, which deploys lightweight AI models in resource-constrained environments for attack detection, evidence collection, and preservation. The framework is evaluated on two datasets, achieving accuracy rates exceeding 99.60% and 99.98% for multiclassification.
A Comprehensive Evaluation on the Benefits of Context Based Password Cracking for Digital Forensics
Journal of Information Security and Applications
This paper evaluates the benefits of context-based password cracking for digital forensics, demonstrating that targeted approaches can increase the likelihood of success when contextual information is available. The study presents an experimental methodology and results section analyzing the approach's performance across ten datasets, proving the impact of context in password cracking.
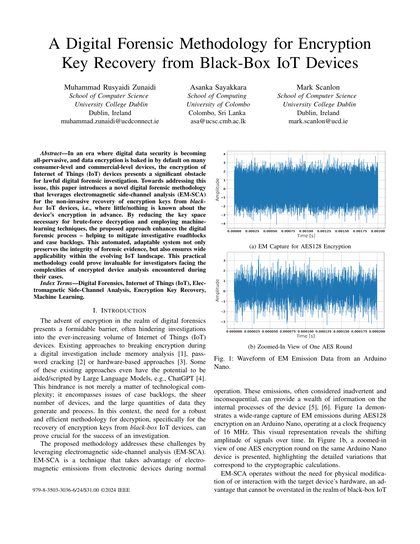
A Digital Forensic Methodology for Encryption Key Recovery from Black-Box IoT Devices
Proceedings of the 12th International Symposium on Digital Forensics and Security
This paper presents a novel digital forensic methodology for recovering encryption keys from black-box IoT devices using electromagnetic side-channel analysis (EM-SCA). The approach leverages machine learning techniques to enhance the digital forensic process, reducing key space and mitigating investigative roadblocks. This automated, adaptable system preserves forensic evidence integrity and ensures wide applicability in the evolving IoT landscape.
A Framework for Integrated Digital Forensic Investigation Employing AutoGen AI Agents
Proceedings of the 12th International Symposium on Digital Forensics and Security
This paper proposes an integrated framework for digital forensic investigations employing AutoGen AI agents and Large Language Models (LLMs) to alleviate investigative workload and shorten the learning curve for investigators. The framework utilizes AI agents and LLMs to perform tasks articulated in natural language by a human agent, addressing the challenges of evolving requirements and information accuracy.
Revealing IoT Cryptographic Settings through Electromagnetic Side-Channel Analysis
Electronics
This study explores the application of Electromagnetic Side-Channel Analysis (EM-SCA) for non-invasively detecting cryptographic settings in IoT devices. The researchers used a machine learning-based approach to identify key lengths and algorithms employed in IoT devices, demonstrating a notable accuracy of 94.55% in distinguishing between AES and ECC operations. This method has significant implications for digital forensic investigations, offering a novel approach for uncovering encrypted data's cryptographic settings.
DFRWS EU 10-Year Review and Future Directions in Digital Forensic Research
Forensic Science International: Digital Investigation Vol. 48 pp. 301685
This study surveys 135 peer-reviewed articles published at the Digital Forensics Research Conference Europe (DFRWS EU) from 2014 to 2023, analyzing co-authorships, geographical spread, and citation metrics to inform future research directions in digital forensic research.
Ensuring Cross-Device Portability of Electromagnetic Side-Channel Analysis for Digital Forensics
Forensic Science International: Digital Investigation Vol. 48 pp. 301684
This study investigates the cross-device portability of Electromagnetic Side-Channel Analysis (EM-SCA) for digital forensics, exploring its applicability to various smart devices. The authors experiment with different devices, including iPhones and Nordic Semiconductor nRF52-DK, and demonstrate the effectiveness of transfer learning techniques in achieving high accuracy.
DFPulse: The 2024 digital forensic practitioner survey
Forensic Science International: Digital Investigation Vol. 51 pp. 301844
This paper presents the results of the largest digital forensic practitioner survey to date, DFPulse, conducted in 2024. The survey collected data from 122 practitioners worldwide, providing insights into their operating environments, technologies used, challenges faced, and future research directions. The study aims to improve collaboration between academia and practitioners, addressing the gap between research and practice in digital forensics.
An Evaluation of AI-Based Network Intrusion Detection in Resource-Constrained Environments
14th Annual IEEE Ubiquitous Computing, Electronics & Mobile Communication Conference (IEEE UEMCON)
This paper evaluates AI-based network intrusion detection in resource-constrained environments, proposing a novel approach that trains and deploys AI models on resource-constrained devices. The approach achieves high classification accuracy, identifying and recording potential malicious attacks in real-time with minimal overhead.
Digital forensic investigation in the age of ChatGPT
Forensic Science International: Digital Investigation Vol. 44 pp. 301543
This editorial discusses the implications of ChatGPT on digital forensic investigation, highlighting both beneficial use cases and potential risks. It explores the use of Large Language Models (LLMs) in generating scripts, question answering, multilingual analysis, and automated sentiment analysis, while also addressing concerns about bias, errors, and overreliance on these systems.
Harder, Better, Faster, Stronger: Optimising the Performance of Context-Based Password Cracking Dictionaries
Forensic Science International: Digital Investigation Vol. 44S pp. 301507
This paper presents a methodology for optimising and ranking contextual wordlists for password cracking, tailored to the suspect in a digital forensic investigation. The approach is evaluated with data leaks from compromised online communities, demonstrating its effectiveness in finding passwords not recovered by traditional methods.
ChatGPT for digital forensic investigation: The good, the bad, and the unknown
Forensic Science International: Digital Investigation Vol. 46 pp. 301609
This paper assesses the impact of ChatGPT on digital forensics, evaluating its capabilities and risks in various use cases, including artefact understanding, evidence searching, code generation, anomaly detection, incident response, and education. The study highlights both the potential benefits and limitations of using ChatGPT in digital forensic investigations, concluding that it can be a useful supporting tool for knowledgeable users but requires careful consideration of its strengths and weaknesses.
Deep Learning Based Network Intrusion Detection System for Resource-Constrained Environments
The 13th EAI International Conference on Digital Forensics and Cyber Crime
This paper presents a deep learning-based network intrusion detection system (IDS) for resource-constrained environments. The proposed 1D-Dilated Causal Neural Network (1D-DCNN) model achieves high accuracy in detecting malicious attacks, outperforming existing deep learning approaches. The model's efficiency and effectiveness make it suitable for resource-constrained environments.
Application of Artificial Intelligence to Network Forensics: Survey, Challenges and Future Directions
IEEE Access Vol. 10
This paper provides a comprehensive survey of the application of artificial intelligence (AI) in network forensics, including expert systems, machine learning, deep learning, and ensemble/hybrid approaches. It discusses the current challenges and future directions in network forensics, covering various application areas such as network traffic analysis, intrusion detection systems, and Internet-of-Things devices.
Data Exfiltration through Electromagnetic Covert Channel of Wired Industrial Control Systems
Applied Sciences Vol. 13 pp. 2928
This study demonstrates a novel attack vector on industrial control systems (ICS) that leverages electromagnetic (EM) radiation from wired Ethernet connections to exfiltrate sensitive information. The attack exploits compromised firmware to encode data into packet transmission patterns, which are then captured and demodulated by an attacker's software-defined radio. This covert channel facilitates data exfiltration from up to two meters away with a 10 bps data rate.
A Novel Dictionary Generation Methodology for Contextual-Based Password Cracking
IEEE Access Vol. 10 pp. 59178-59188
This paper introduces a novel dictionary generation methodology for contextual-based password cracking, enabling the creation of custom dictionary word lists for dictionary-based password cracking attacks. The approach leverages contextual information encountered during an investigation, such as user habits and personal information, to generate targeted password candidates. This methodology has the potential to expedite password cracking processes in law enforcement investigations.
Security, Ethics and Privacy Issues in Remote Extended Reality for Education
Mixed Reality for Education
This chapter explores security, ethics, and privacy concerns in remote extended reality learning environments, highlighting the need for a comprehensive approach to address these issues in immersive education.
Identifying Internet of Things Software Activities using Deep Learning-based Electromagnetic Side-Channel Analysis
Forensic Science International: Digital Investigation Vol. 39 pp. 301308
This study explores the application of machine learning techniques to identify complex activities on IoT devices using electromagnetic side-channel analysis. The researchers created a dataset by running ten sorting algorithms on an Arduino device and used it to train various classification models, including deep learning models. The results show that convolutional neural networks can accurately predict the activity being executed with a high level of accuracy (99.6%).
PCWQ: A Framework for Evaluating Password Cracking Wordlist Quality
The 12th EAI International Conference on Digital Forensics and Cyber Crime
This paper presents PCWQ, a novel framework for evaluating the quality of password cracking wordlists. The framework assesses wordlists based on several interconnecting metrics, including final percentage of passwords cracked, number of guesses until target, progress over time, size of wordlist, and better performance with stronger passwords. The authors conduct a preliminary analysis to demonstrate the framework's evaluation process.
How Viable is Password Cracking in Digital Forensic Investigation? Analyzing the Guessability of over 3.9 Billion Real-World Accounts
Forensic Science International: Digital Investigation Vol. 37 pp. 301186
This study analyzed over 3.9 billion real-world passwords to assess their guessability and identify patterns in password construction. The analysis reveals that certain semantic classes are more common than others, indicating the importance of user context in password selection. The study also evaluates the effectiveness of password cracking tools and techniques, providing insights for digital investigators.
A Comparative Study of Support Vector Machine and Neural Networks for File Type Identification Using n-gram Analysis
Forensic Science International: Digital Investigation
This study compares the performance of Support Vector Machines (SVMs) and Neural Networks (NNs) for file type identification using n-gram analysis. The authors investigate the influence of input parameters, such as learning rate and n-gram values, on the results and compare the scalability of SVMs and NNs. The study finds that SVM-based approaches perform better than NNs, but their scalability is still a challenge.
TraceGen: User Activity Emulation for Digital Forensic Test Image Generation
Forensic Science International: Digital Investigation
This paper presents TraceGen, an automated system for generating realistic digital forensic test images through user activity emulation. The framework consists of a series of actions contained within scripts that are executed both externally and internally to a target virtual machine. TraceGen aims to address the issue of emulating user activities and behaviours, ensuring forensically realistic traces are created in the resulting test images.
Vec2UAge: Enhancing Underage Age Estimation Performance through Facial Embeddings
Forensic Science International: Digital Investigation
This paper presents Vec2UAge, a novel regression-based model for estimating the age of underage individuals from facial embeddings. The model is trained on the VisAGe and Selfie-FV datasets and achieves a mean absolute error rate of 2.36 years. The authors evaluate the impact of random initializations, optimizers, and learning rates on the model's performance.
On Offloading Network Forensic Analytics to Programmable Data Plane Switches
Book Series: World Scientific Series in Digital Forensics and Cybersecurity
This paper proposes a novel approach to network forensic analytics by leveraging programmable data plane switches to detect and mitigate Distributed Denial of Service (DDoS) attacks and Internet of Things (IoT) device misuse. The authors implement two switch-based use cases to conduct network forensics at line rate, reducing latency and improving incident response.
A Survey Exploring Open Source Intelligence for Smarter Password Cracking
Forensic Science International: Digital Investigation Vol. 35 pp. 301075
This paper explores the potential of Open Source Intelligence (OSINT) for more efficient password cracking in digital investigations. A comprehensive survey of password strength, cracking, and OSINT is presented, along with an analysis of password structure and demographic factors influencing password selection. The authors discuss the challenges of password cracking and the potential impact of OSINT on law enforcement.
Retracing the Flow of the Stream: Investigating Kodi Streaming Services
The 11th EAI International Conference on Digital Forensics and Cyber Crime
This paper presents a new method for quickly locating Kodi artifacts and gathering information for successful prosecution of digital piracy and streaming of illegal content. The approach is evaluated on Windows, Android, and Linux platforms, demonstrating the location of file artifacts, databases, and viewed content history.
SoK: Exploring the State of the Art and the Future Potential of Artificial Intelligence in Digital Forensic Investigation
The 13th International Workshop on Digital Forensics (WSDF), held at the 15th International Conference on Availability, Reliability and Security (ARES)
This systematic overview of artificial intelligence (AI) in digital forensic investigation explores the current state of the art and future potential of AI in expediting digital forensic analysis and increasing case processing capacities. The authors discuss AI applications in data discovery, device triage, and other areas, highlighting current challenges and future directions.
Facilitating Electromagnetic Side-Channel Analysis for IoT Investigation: Evaluating the EMvidence Framework
Forensic Science International: Digital Investigation
This paper presents the EMvidence framework, a software tool that facilitates electromagnetic side-channel analysis for IoT investigation. The framework automates and simplifies the process of acquiring and analyzing electromagnetic signals from IoT devices, making it accessible to digital forensic investigators without specialized equipment or expertise.
Assessing the Influencing Factors on the Accuracy of Underage Facial Age Estimation
The 6th IEEE International Conference on Cyber Security and Protection of Digital Services (Cyber Security)
This study evaluates the influencing factors on the accuracy of underage facial age estimation using two cloud services, Microsoft Azure's Face API and Amazon Web Service's Rekognition service. The analysis of the VisAGe dataset reveals correlations between facial attributes and age estimation errors, identifying the most significant factors to be addressed in future age estimation modeling.
Automated Artefact Relevancy Determination from Artefact Metadata and Associated Timeline Events
The 6th IEEE International Conference on Cyber Security and Protection of Digital Services (Cyber Security)
This paper presents an approach for automated artefact relevancy determination from artefact metadata and associated timeline events. The method uses a relevancy score to rank file artefacts by likely relevance, based on data reduction techniques and machine learning models. The approach is validated through experimentation with three emulated investigation scenarios, demonstrating its potential to aid investigators in the discovery and prioritisation of evidence.
Smarter Password Guessing Techniques Leveraging Contextual Information and OSINT
6th IEEE International Conference on Cyber Security and Protection of Digital Services (Cyber Security)
This paper proposes smarter password guessing techniques that leverage contextual information and Open Source Intelligence (OSINT) to improve password recovery rates. The authors explore the use of OSINT to gather information about a suspect's online and offline life, which can be used to make educated guesses about their password. The research aims to create a bespoke, personalized dictionary list to feed into password cracking tools.
Cutting through the Emissions: Feature Selection from Electromagnetic Side-Channel Data for Activity Detection
Forensic Science International: Digital Investigation Vol. 32 pp. 300927
This paper presents a systematic methodology to identify information leaking frequency channels from high dimensional EM data using multiple filtering techniques and machine learning. The approach is evaluated on a dataset of EM signals from an IoT device, demonstrating its effectiveness in reducing the number of channels from 20,000 to less than 100, improving real-time analysis efficiency.
DeepUAge: Improving Underage Age Estimation Accuracy to Aid CSEM Investigation
Forensic Science International: Digital Investigation Vol. 32 pp. 300921
DeepUAge improves underage age estimation accuracy to aid Child Sexual Exploitation Material (CSEM) investigation. The model, trained on the VisAGe dataset, achieves state-of-the-art performance for age estimation of minors, with a mean absolute error (MAE) rate of 2.73 years. This work tackles the challenges of collecting and annotating underage facial age data, and its application can expedite digital investigations.
EMvidence: A Framework for Digital Evidence Acquisition from IoT Devices through Electromagnetic Side-Channel Analysis
Forensic Science International: Digital Investigation Vol. 32 pp. 300907
This paper presents EMvidence, a software framework for digital forensic investigators to acquire evidence from IoT devices through electromagnetic side-channel analysis. The framework automates and performs electromagnetic side-channel evidence collection, making it a practical reality for digital forensic investigators.
Improving Borderline Adulthood Facial Age Estimation through Ensemble Learning
The 8th International Workshop on Cyber Crime (IWCC), held at the 14th International Conference on Availability, Reliability and Security (ARES)
This paper presents an ensemble learning approach to improve facial age estimation for borderline adulthood cases. The authors develop a deep learning model (DS13K) and fine-tune it on the Deep Expectation (DEX) model to achieve an accuracy of 68% for the age group 16-17 years old, outperforming DEX by 4 times. The study also evaluates existing cloud-based facial age prediction services.
Methodology for the Automated Metadata-Based Classification of Incriminating Digital Forensic Artefacts
The 12th International Workshop on Digital Forensics (WSDF), held at the 14th International Conference on Availability, Reliability and Security (ARES)
This paper proposes a methodology for automatically prioritizing suspicious file artefacts in digital forensic investigations, leveraging a supervised machine learning approach and a toolkit for data extraction from disk images. The methodology aims to reduce manual analysis effort and improve the efficiency of the investigative process.
A Survey of Electromagnetic Side-Channel Attacks and Discussion on their Case-Progressing Potential for Digital Forensics
Digital Investigation Vol. 29 pp. 43-54
This paper surveys electromagnetic side-channel attacks and their potential for digital forensics on IoT devices. It discusses the challenges of analyzing encrypted data from IoT devices and explores the use of electromagnetic side-channel analysis to recover cryptographic keys and other sensitive information.
Leveraging Electromagnetic Side-Channel Analysis for the Investigation of IoT Devices
Digital Investigation
This paper presents a novel methodology to inspect the internal software activities of IoT devices through their electromagnetic radiation emissions during live device investigation. The approach uses electromagnetic side-channel analysis (EM-SCA) to detect software activities, including cryptographic algorithms and malicious modifications, with high accuracy.
Shining a light on Spotlight: Leveraging Apple's desktop search utility to recover deleted file metadata on macOS
Digital Investigation
This study examines Apple's desktop search technology, Spotlight, to recover deleted file metadata on macOS. Researchers developed a novel approach to extract persistent records of deleted files directly from the Spotlight database and recover records from deleted database pages in unused space. The study provides a proof-of-concept implementation and discusses the forensic opportunities offered by recovering records for deleted files within the database and unused space on the filesystem.
Solid State Drive Forensics: Where Do We Stand?
Digital Forensics and Cyber Crime pp. 149-164
This paper examines the current state of solid-state drive (SSD) forensics, addressing the challenges posed by SSDs' background data movement and garbage collection processes. The authors investigate the impact of TRIM, data volume, and powered-on time on data recovery and provide guidance on extracting artefacts from SSDs under various conditions.
Accuracy Enhancement of Electromagnetic Side-channel Attacks on Computer Monitors
The Second International Workshop on Criminal Use of Information Hiding (CUING), part of the 13th International Conference on Availability, Reliability and Security (ARES)
This paper investigates the accuracy of electromagnetic side-channel attacks on computer monitors, focusing on factors beyond sampling rate and bandwidth. The authors evaluate noise removal, image blending, and image quality adjustments to improve image reconstruction accuracy, exploring avenues for future improvements in EM side-channel attacks.
Deduplicated Disk Image Evidence Acquisition and Forensically-Sound Reconstruction
Proceedings of the 17th IEEE International Conference On Trust, Security And Privacy In Computing And Communications (TrustCom-18) pp. 1674-1679
This paper presents a system for deduplicated disk image evidence acquisition and forensically-sound reconstruction, addressing the growing digital evidence backlog in law enforcement. The system enables automated, centralized acquisition and analysis, reducing storage and bandwidth requirements, and facilitating non-expert evidence processing.
Enabling the Non-Expert Analysis of Large Volumes of Intercepted Network Traffic
Advances in Digital Forensics XIV pp. 183-197
This paper proposes a novel approach to analyze large volumes of intercepted network traffic based on network metadata, reducing analysis duration and providing insights for non-technical investigators. The approach is tested with a large sample of network traffic data and can be used to identify devices and usage behind an internet connection.
Deep Learning at the Shallow End: Malware Classification for Non-Domain Experts
Digital Investigation Vol. 26 pp. S118 - S126
This paper presents a deep learning-based malware classification approach that requires no expert domain knowledge and is based on a purely data-driven approach for complex pattern and feature identification. The model achieves a high accuracy of 98.2% in classifying raw binary files into one of 9 classes of malware, with a processing time of 0.02 seconds per file.
Digital Forensic Investigation of Two-Way Radio Communication Equipment and Services
Digital Investigation Vol. 26S pp. xx-xx
This study investigates the digital forensic traces in modern two-way radio communication equipment and services, which is crucial for law enforcement in crime investigations. The research proposes a novel workflow for investigators to follow when encountering such equipment, highlighting the need for knowledge about radio communication equipment, infrastructure, and associated services.
Digital Forensic Investigation of Two-Way Radio Communication Equipment and Services
Digital Investigation Vol. 26 pp. S77 - S86
This paper investigates the digital forensic investigation of two-way radio communication equipment and services, including the acquisition and analysis of digital traces in modern radio communication devices. The authors propose a workflow for radio device investigation and evaluate the possibility of using popular forensic tools to acquire artefacts from radio communication equipment.
Electromagnetic Side-Channel Attacks: Potential for Progressing Hindered Digital Forensic Analysis
Proceedings of the International Workshop on Speculative Side Channel Analysis (WoSSCA 2018)
This paper explores the potential of electromagnetic side-channel analysis in progressing hindered digital forensic investigations. The authors argue that EM side-channel attacks can provide a hands-off approach to accessing internal device information, overcoming encryption and limited standardization of IoT devices.
Evaluating Automated Facial Age Estimation Techniques for Digital Forensics
12th International Workshop on Systematic Approaches to Digital Forensics Engineering (SADFE), IEEE Security & Privacy Workshops
This paper evaluates existing automated facial age estimation techniques for digital forensics, highlighting their limitations and proposing a dataset generator to overcome the lack of sufficient sample images in specific age ranges. The study assesses the performance of offline and cloud-based models, releasing a tool to generate uniformly distributed random images by age and gender.
Hierarchical Bloom Filter Trees for Approximate Matching
Journal of Digital Forensics, Security and Law Vol. 13 pp. 81-96
This paper proposes the use of Hierarchical Bloom Filter Trees (HBFTs) to improve the runtime efficiency of approximate matching techniques in digital forensics. HBFTs reduce the number of pairwise comparisons required, achieving substantial speed gains while maintaining effectiveness. The authors evaluate the effectiveness of HBFTs using the MRSH-v2 algorithm and explore the effects of different configurations of HBFTs.
Expediting MRSH-v2 Approximate Matching with Hierarchical Bloom Filter Trees
Digital Forensics and Cyber Crime. ICDF2C 2017 Vol. 216 pp. 144-157
This paper presents an improvement to the MRSH-v2 approximate matching algorithm using Hierarchical Bloom Filter Trees (HBFT) to expedite the search process for digital forensic investigators. Experiments demonstrate substantial speed gains over the original MRSH-v2 while maintaining effectiveness.
Private Web Browser Forensics: A Case Study on Epic Privacy Browser
Journal of Information Warfare Vol. 17
This study examines the Epic Privacy Browser, a private web browser designed to protect users' privacy, and its potential for forensic analysis. The researchers investigate the types of evidence left behind by the browser on Windows 10 and Windows 7 operating systems, including live and post-mortem analysis. The study aims to identify the tools and methods for effective analysis of the browser's artefacts.
Data Analytics for Digital Forensics and Cybersecurity
Predict Conference; Europe's Leading Data Conference (Predict 2017)
This paper addresses the problem of information overload in digital forensics and cybersecurity by proposing a data analytics approach for intelligent, real-time, automated data processing and event categorization. The solution aims to combat the increasing frequency and sophistication of cyberattacks by reducing false positive alerts in network intrusion detection systems.
Privileged Data within Digital Evidence
Proceedings of the 16th IEEE International Conference On Trust, Security And Privacy In Computing And Communications (TrustCom-17) pp. 737-744
This paper presents a script for handling privileged data in digital forensic tools, specifically in Nuix, to minimize exposure to investigators and automate the filtering process. The script increases effectiveness by relating files based on content, addressing the limitations of traditional filtering methods.
Evaluation of Digital Forensic Process Models with Respect to Digital Forensics as a Service
Proceedings of the 16th European Conference on Cyber Warfare and Security (ECCWS 2017) pp. 573-581
This paper evaluates the applicability of existing digital forensic process models to a cloud-based evidence processing paradigm, specifically Digital Forensics as a Service (DFaaS). The authors analyze the characteristics of each current process model and review the benefits of DFaaS, aiming to expedite the investigative process and reduce costs.
Forensic Analysis of Epic Privacy Browser on Windows Operating Systems
Proceedings of the 16th European Conference on Cyber Warfare and Security (ECCWS 2017) pp. 341-350
This paper presents a forensic analysis of Epic Privacy Browser on Windows operating systems, focusing on the identification and analysis of artefact evidence left on Windows 10 compared to Windows 7. The study aims to establish if the introduction of Windows 10 has had an adverse effect on the browser's claim of clearing all user activity traces upon closure.
Integration of Ether Unpacker into Ragpicker for plugin-based Malware Analysis and Identification
Proceedings of the 16th European Conference on Cyber Warfare and Security (ECCWS 2017) pp. 419-425
This paper presents a new approach to malware analysis by integrating Ether Unpacker into the plugin-based malware analysis tool, Ragpicker. The integration aims to improve the unpacking rate of malware samples, enabling the analysis of transferred and reused code. The authors evaluate their approach against real-world malware patterns, demonstrating its effectiveness in identifying malware variants and families.
Behavioral Service Graphs: A Formal Data-Driven Approach for Prompt Investigation of Enterprise and Internet-wide Infections
Digital Investigation Vol. 20S pp. 47-55
This paper proposes Behavioral Service Graphs, a formal data-driven approach for prompt investigation of enterprise and internet-wide infections. It leverages probing activities to rapidly infer infections and models infected machines as graphs to infer and correlate distributed groups of infected machines.
EviPlant: An Efficient Digital Forensic Challenge Creation, Manipulation, and Distribution Solution
Digital Investigation Vol. 20S pp. 29-36
EviPlant is a system designed to efficiently create, manipulate, store, and distribute digital forensic challenges for education and training. It allows educators to create evidence packages that can be integrated with base images, reducing the need for large, full-image files and making it easier to distribute challenges to students.
Behavioral Service Graphs: A Big Data Approach for Prompt Investigation of Internet-wide Infections
Proceedings of the IFIP International Workshop on Cybercrime Investigation and Digital Forensics (CID) pp. 1-5
This paper proposes Behavioral Service Graphs, a proactive approach to generating network-based evidence for network forensic investigation. It leverages big data behavioral analytics and graph theoretical concepts to infer and correlate groups of compromised network machines, providing actionable insights for prompt mitigation and further analysis.
Towards the Leveraging of Data Deduplication to Break the Disk Acquisition Speed Limit
Proceedings of the IFIP International Workshop on Cybercrime Investigation and Digital Forensics (CID) pp. 1-5
This paper proposes a data deduplication system to expedite digital forensic evidence acquisition and analysis. The system leverages a deduplicated forensic data storage system to eliminate unnecessary reacquisition and analysis of previously processed data, reducing acquisition time and improving the overall efficiency of the digital forensic process.
Battling the Digital Forensic Backlog
Proceedings of the 2nd International Workshop on Cloud Security and Forensics (WCSF 2016) pp. 10-14
This paper discusses the growing digital forensic backlog faced by law enforcement agencies due to the increasing number of digital devices involved in investigations. It highlights the challenges in identifying, acquiring, storing, and analyzing digital evidence from various sources, including cloud-based services and IoT devices. The author proposes future research directions to improve the efficiency of the digital forensic process.
Battling the Digital Forensic Backlog through Data Deduplication
Proceedings of the 6th IEEE International Conference on Innovative Computing Technologies (INTECH 2016)
This paper proposes a novel solution to combat the digital forensic backlog through data deduplication. The solution leverages a centralized storage system to store a single copy of each object, eliminating redundant storage and reanalysis of previously processed data. This approach can reduce storage requirements, expedite digital forensic processing, and facilitate collaborative examination and sharing of digital evidence.
IPv6 Security and Forensics
2nd International Workshop on Cloud Security and Forensics (WCSF 2016) pp. 743-748
This paper presents a new approach to investigate IPv6 network attacks with case studies, focusing on IPv6 security and forensics. It discusses different types of IPv6 attacks and provides a comprehensive overview of IPv6 network attack techniques, including reconnaissance, exploitation, and mitigation strategies.
An Analytical Approach to the Recovery of Data From 3rd Party Proprietary CCTV File Systems
15th European Conference on Cyber Warfare and Security (ECCWS 2016)
This paper presents an analytical approach to recovering data from 3rd party proprietary CCTV file systems, focusing on a Ganz CCTV DVR model C-MPDVR-16. The authors reverse engineer the proprietary file system, enabling the retrieval of the oldest video footage possible. The method is evaluated using a case study, demonstrating the feasibility of recovering video footage from a DVR with no initial knowledge or documentation available.
Current Challenges and Future Research Areas for Digital Forensic Investigation
The 11th ADFSL Conference on Digital Forensics, Security and Law (CDFSL 2016) pp. 9-20
This paper explores the current challenges in digital forensic investigations, including the digital evidence backlog, and outlines future research areas to improve the process. The authors discuss the increasing complexity, diversity, and volume of digital evidence, as well as the need for standardization and automation in digital forensic tools and processes.
Increasing Digital Investigator Availability through Efficient Workflow Management and Automation
The 4th International Symposium on Digital Forensics and Security (ISDFS 2016) pp. 68-73
This paper proposes a workflow management automation framework to streamline digital investigation workflows, reducing time spent on acquisition and preparation steps, and increasing efficiency of forensic software and hardware use. The framework is evaluated in a real-world scenario, demonstrating its benefits and robustness.
On the Benefits of Information Retrieval and Information Extraction Techniques Applied to Digital Forensics
Advanced Multimedia and Ubiquitous Engineering: FutureTech & MUE pp. 641-647
This paper explores the application of Information Retrieval (IR) and Information Extraction (IE) techniques to digital forensics, highlighting their potential to improve the efficiency and effectiveness of investigations. The authors discuss the benefits of cloud-based digital forensic investigation platforms and the importance of precision and recall in different stages of an investigation.
Tiered Forensic Methodology Model for Digital Field Triage by Non-Digital Evidence Specialists
Digital Investigation Vol. 16 pp. 75-85
This paper presents a tiered forensic methodology model for digital field triage by non-digital evidence specialists. The model aims to increase investigation efficiency and reduce the backlog of digital evidence waiting for analysis by trained specialists. The authors propose a framework for training front-line investigators to conduct digital field triage, allowing them to provide actionable information quickly and maintain the integrity of digital evidence.
An Evaluation of Google Plus Communities as an Active Learning Journal Alternative to Improve Learning Efficacy
Proceedings of 8th International Conference on Engaging Pedagogy (ICEP 2015)
This study evaluates Google Plus Communities as an active learning journal alternative to improve learning efficacy. The authors present guidelines for deploying G+ Communities in educational settings, highlighting their potential to foster collaborative learning, social interaction, and community engagement.
Forensic Analysis and Remote Evidence Recovery from Syncthing: An Open Source Decentralised File Synchronisation Utility
Digital Forensics and Cyber Crime Vol. 157 pp. 85-99
This paper presents a forensic analysis and remote evidence recovery techniques for Syncthing, an open-source decentralized file synchronization utility. The authors outline the entry points for a Syncthing investigation, describe the network communication protocol, and develop a proof-of-concept tool for remote evidence recovery. The study addresses the need for digital forensics procedures to keep pace with decentralized services like Syncthing.
Network Investigation Methodology for BitTorrent Sync: A Peer-to-Peer Based File Synchronisation Service
Computers & Security Vol. 54 pp. 27 - 43
This paper proposes a network investigation methodology for BitTorrent Sync, a peer-to-peer file synchronization service, to aid in the control of data flow across security perimeters. The methodology includes recommendations for investigating various scenarios, including legitimate and illicit activities.
Project Maelstrom: Forensic Analysis of the BitTorrent-Powered Browser
Journal of Digital Forensics, Security and Law: Proc. of 10th International Conference on Systematic Approaches to Digital Forensic Engineering (SADFE 2015) pp. 115-124
This paper presents a forensic analysis of Project Maelstrom, a decentralized web browser powered by BitTorrent. The authors explore the browser's functionality, forensic value, and the evidence it leaves behind, including installation and configuration files, user data, and torrent-related settings.
Overview of the Forensic Investigation of Cloud Services
10th International Conference on Availability, Reliability and Security (ARES 2015) pp. 556-565
This paper provides an overview of the forensic investigation of cloud services, discussing the challenges and opportunities of cloud computing in digital forensics. It examines the state-of-the-art in cloud-focused digital forensic practices, including the collection and analysis of evidence, and the potential use of cloud technologies to provide Digital Forensics as a Service.
Remote Evidence Acquisition
Proceedings of the International Workshop on Digital Forensics (WSDF 2015)
This paper presents a novel approach to remote evidence acquisition in digital forensics. The authors propose a method for collecting and preserving digital evidence from remote locations, addressing the challenges of on-site collection. The contribution is a framework for secure and efficient evidence transfer, enhancing the integrity and admissibility of digital evidence in investigations.
Towards the Forensic Identification and Investigation of Cloud Hosted Servers through Noninvasive Wiretaps
Proceedings of 10th International Conference on Availability, Reliability and Security (ARES 2015)
This paper presents a new approach to rapidly and reliably identify cloud-hosted servers through non-invasive wiretaps. A handheld device composed of an embedded computer and a method of undetectable Ethernet-based communication interception is developed and tested. The device captures minimal information and only stores relevant data, with an audit log of operator actions for reporting.
HTML5 Zero Configuration Covert Channels: Security Risks and Challenges
The 10th ADFSL Conference on Digital Forensics, Security and Law (CDFSL 2015) pp. 135-150
This paper explores the security risks and challenges of HTML5 zero-configuration covert channels, including the potential for cybercriminals to use these services for illegal activities. The authors analyze the forensic consequences of these services and propose methods for retrieving evidence.
An analysis of BitTorrent cross-swarm peer participation and geolocational distribution
23rd International Conference on Computer Communication and Networks (ICCCN 2014) pp. 1-6
This paper analyzes BitTorrent cross-swarm peer participation and geolocational distribution. The authors collected 2 terabytes of data from 16 swarms of popular TV shows, identifying 6.3 million distinct IPs. The study found significant cross-swarm participation and geolocational distribution, with Australia, Europe, and North America playing a crucial role in influencing swarm size. The results can aid in network usage prediction, bandwidth provisioning, and future network design.
BitTorrent Sync: Network Investigation Methodology
Proceedings of 9th International Conference on Availability, Reliability and Security (ARES 2014) pp. 21-29
This paper presents a network investigation methodology for BitTorrent Sync, a decentralized file replication utility, to aid digital forensic investigations. The authors propose a framework for retrieving digital evidence from the network and provide results from a proof-of-concept investigation.
Leveraging Decentralisation to Extend the Digital Evidence Acquisition Window: Case Study on BitTorrent Sync
Journal of Digital Forensics, Security and Law: Proc. of Sixth International Conference on Digital Forensics & Cyber Crime (ICDF2C 2014) pp. 85-99
This paper presents a methodology for the remote recovery and verification of digital evidence from decentralized file synchronization services, specifically BitTorrent Sync. The authors outline a proof-of-concept implementation and discuss the challenges and opportunities of remote digital evidence retrieval in the context of mobile devices and cloud-based services.
Digital Evidence Bag Selection for P2P Network Investigation
Proceedings of the 7th International Symposium on Digital Forensics and Information Security (DFIS-2013), Future Information Technology, Application, and Service pp. 307-314
This paper proposes a new digital evidence bag format for P2P network investigations, addressing the limitations of existing formats in handling network traffic and metadata. The proposed format incorporates network byte streams and on-the-fly metadata generation to expedite identification and analysis.
BitTorrent Sync: First Impressions and Digital Forensic Implications
Digital Investigation Vol. 11, Supplement 1 pp. S77-S86
This paper presents a forensic analysis of BitTorrent Sync, a decentralized file synchronization service, and its implications for digital investigations. The authors examine the client application, network traffic, and artefacts created during installation and use, providing valuable insights for digital forensic investigators.
The Case for a Collaborative Universal Peer-to-Peer Botnet Investigation Framework
Proceedings of the 9th International Conference on Cyber Warfare and Security (ICCWS 2014) pp. 287-293
This paper proposes a collaborative universal peer-to-peer botnet investigation framework to fast-track the investigative process through collaboration between key stakeholders. The framework exploits common attributes of P2P networks, including intra-peer communication, self-propagation, and node maintenance, to identify and record communication patterns. This enables the elimination of duplicated work by forensic investigators and facilitates the investigation of any known botnet and adaptation to new networks.
Study of Peer-to-Peer Network Based Cybercrime Investigation: Application on Botnet Technologies
PhD Thesis
This PhD thesis explores the investigation of Peer-to-Peer (P2P) networks, which are vulnerable to cybercrimes such as botnet propagation and malware distribution. The Universal P2P Network Investigation Framework (UP2PNIF) is introduced to facilitate faster and more efficient investigations of P2P networks.
Investigating Cybercrimes That Occur on Documented P2P Networks
Pervasive and Ubiquitous Technology Innovations for Ambient Intelligence Environments pp. 109-115
This paper presents a methodology for investigating cybercrimes on documented P2P networks, specifically BitTorrent, by analyzing the top 100 most popular swarms over a one-week period. The investigation aims to quantify the scale of unauthorized distribution of copyrighted material and identify the geographical distribution of peers involved.
Universal Peer-to-Peer Network Investigation Framework
Availability, Reliability and Security (ARES), 2013 Eighth International Conference on pp. 694-700
This paper introduces the Universal Peer-to-Peer Network Investigation Framework (UP2PNIF), a tool for investigating P2P networks. The framework exploits common attributes of P2P networks to enable faster and less labor-intensive investigations. It can be used for various investigation types, including evidence collection, anatomy, wide-area measurement, and takeover.
Peer-to-Peer Botnet Investigation: A Review
Proceedings of the 6th International Symposium on Digital Forensics and Information Security (DFIS-2012), Future Information Technology, Application, and Service," pp. 231-238
This paper reviews the state-of-the-art in Peer-to-Peer (P2P) botnet investigation, highlighting the challenges and obstacles faced by investigators. It discusses the evolution of botnet design from traditional client/server to decentralized P2P networks, and the implications for investigation and takedown. The paper outlines three main approaches to P2P botnet investigation and presents case studies of the Nugache, Storm, and Waledec botnets.
Investigating Cybercrimes That Occur on Documented P2P Networks
International Journal of Ambient Computing and Intelligence Vol. 3 pp. 56-63
This paper presents a methodology for investigating cybercrimes on documented P2P networks, specifically BitTorrent, by analyzing the top 100 most popular swarms over a one-week period. The investigation aims to quantify the scale of unauthorized distribution of copyrighted material through BitTorrent.
A week in the Life of the Most Popular BitTorrent Swarms
Proceedings of the 5th Annual Symposium on Information Assurance (ASIA 2010) pp. 32-36
This paper presents an analysis of the most popular BitTorrent swarms over a week, focusing on the scale of unauthorized distribution of copyrighted material. The investigation collected data on 8,489,287 unique IP addresses, with 50.6% of files split into smaller chunks for distribution. The results show a global distribution of peers, with the US, UK, India, and Canada being the top countries detected.
Enabling the Remote Acquisition of Digital Forensic Evidence through Secure Data Transmission and Verification
MSc Thesis
This thesis presents RAFT, a system for remote acquisition of digital forensic evidence through secure data transmission and verification. RAFT enables law enforcement officers to transfer images from suspect computers to forensic labs for analysis, reducing investigation time and ensuring court-admissible evidence.
Online Acquisition of Digital Forensic Evidence
Proceedings of International Conference on Digital Forensics and Cyber Crime (ICDF2C 2009) pp. 122-131
This paper introduces RAFT, a remote forensic hard drive imaging tool designed to reduce the time wasted by forensic investigators in collecting digital evidence. RAFT enables law enforcement officers to remotely transfer images of suspect computers to a forensic laboratory for analysis, ensuring court-admissible evidence through secure and verifiable client/server imaging architecture.